Secure Overlay Networking for Redis on the Akash Network - PART-1
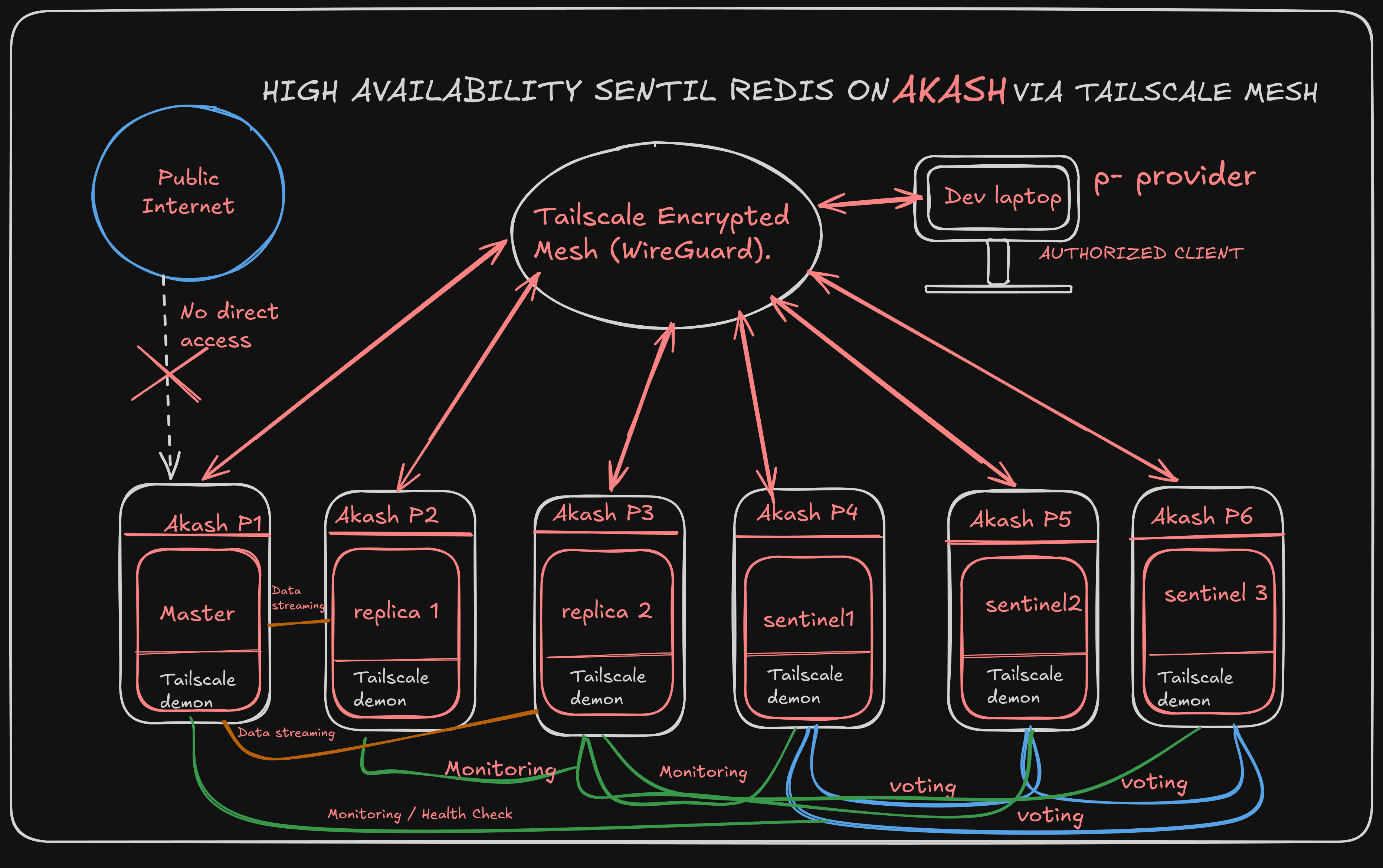
When deploying on the Akash Network, builders unlock access to a global, decentralized marketplace of compute. However, shifting stateful workloads—like a High-Availability Redis cluster from traditional centralized clouds (like AWS or GCP or AZURE) to decentralized providers requires a paradigm shift in how we handle networking.
In a traditional cloud, you rely on a Virtual Private Cloud (VPC) to isolate your databases. On Akash, your compute leases might be distributed across multiple independent providers globally. There is no native, cross-provider VPC.
To achieve enterprise-grade security and reliable connectivity for stateful databases on Akash, we must decouple the network from the physical infrastructure. This first part of the masterclass covers how to build a Zero-Trust, encrypted overlay network using Tailscale within your Akash SDL (Stack Definition Language).
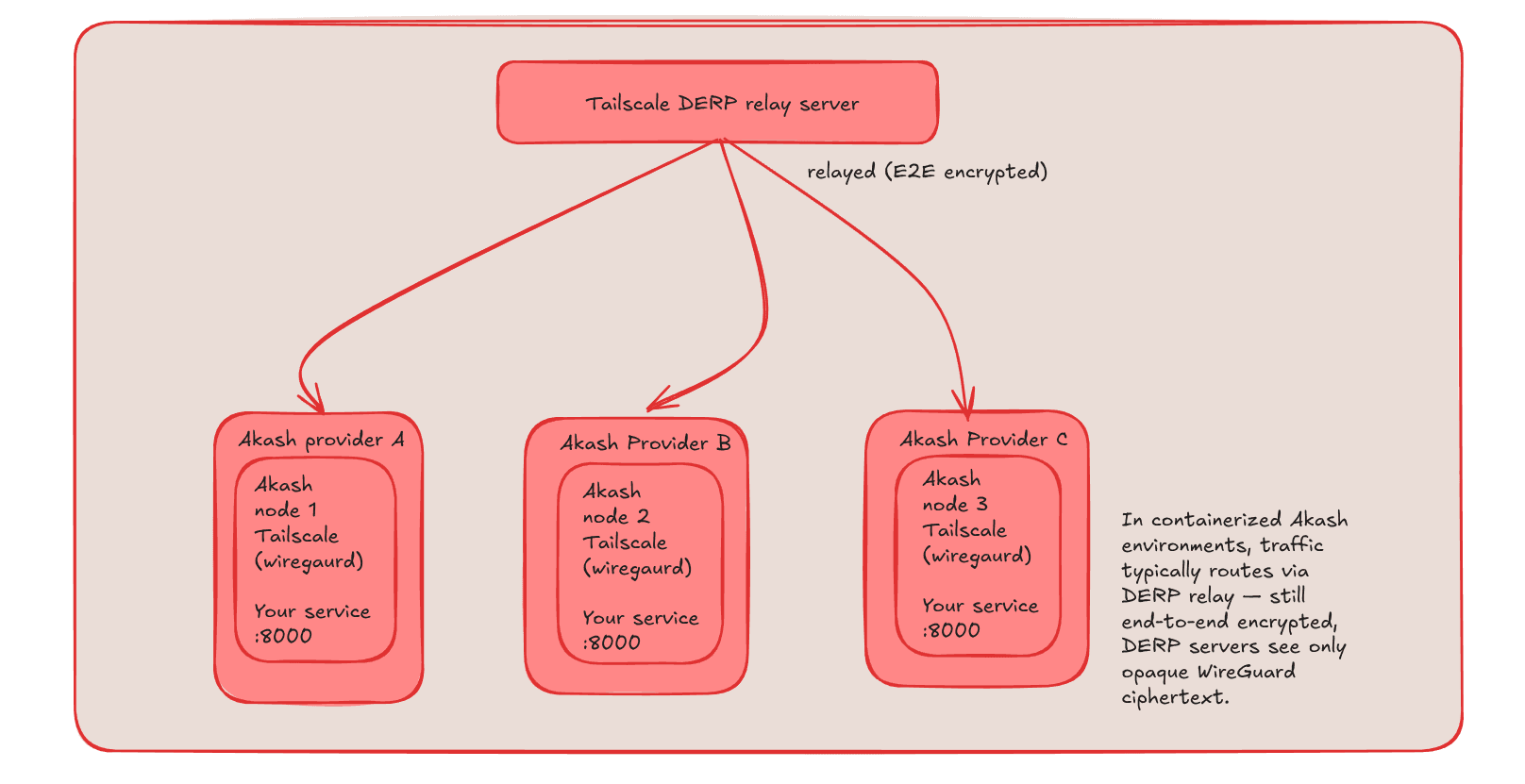
1. The Architecture: Bridging Decentralized Providers
When deploying a distributed database, the nodes must communicate with each other seamlessly. If a Redis Master is leased from a provider in North America and a Replica is leased from a provider in Europe, they cannot safely communicate over the open internet without an encryption layer.
An overlay network acts as a dynamic, software-defined VPC that travels directly inside your Akash containers.
By installing a mesh VPN (like Tailscale) inside the deployment, we achieve three architectural goals crucial for the Akash ecosystem:
End-to-End Encryption: All database replication and gossip protocols are routed through WireGuard tunnels, completely hidden from the underlying provider.
Provider Agnosticism: Containers communicate using static
100.x.x.xmesh IPs. You can close a lease, spin up a new one on a completely different provider, and the mesh network will seamlessly re-route the traffic.Zero-Trust Access: The database ports do not need to be exposed in the
exposeblock of your Akash SDL, making them invisible to the public internet.
2. Securing the Database: Localhost Isolation on Public Compute
A common oversight when deploying Redis on public cloud infrastructure is leaving the default binding open. Configuring bind 0.0.0.0 tells the Redis process to listen for incoming connections on all available network interfaces.
From a Site Reliability Engineering perspective, the most secure database on decentralized compute is one that refuses to talk to the network at all.
We achieve absolute isolation by restricting Redis strictly to the container's loopback interface:
# /etc/redis/redis.conf
bind 127.0.0.1
requirepass <YOUR_STRONG_PASSWORD> # Instead of using only requirepass, using ACL is a better security practice.
By binding to 127.0.0.1, Redis is now completely blind to the outside world and the underlying provider's network. It will only accept connections originating from inside its own container. We then use Tailscale to build a secure bridge into this isolated environment.
3. The Mesh Overlay: Userspace Networking on Akash
For security reasons, Akash providers drop elevated kernel privileges. This means containers do not have access to /dev/net/tun, which traditional VPNs require. To bypass this, we run the Tailscale daemon in userspace networking mode.
Once the node is authenticated to the mesh, we need a way to pass the encrypted mesh traffic to our isolated Redis instance. We use tailscale serve, a lightweight, built-in reverse proxy.
Here is the exact boot sequence to include in your deployment script:
# 1. Start Tailscale in Userspace Mode
tailscaled --tun=userspace-networking --socks5-server=localhost:1055 &
# 2. Authenticate the Node to the Mesh Network
tailscale up --authkey=\(TS_AUTHKEY --hostname=\)NODE_HOSTNAME --accept-dns=true
# 3. Route Mesh Traffic to the Local Database
tailscale serve --tcp=6379 127.0.0.1:6379
# 4. Start Redis in the background
proxychains4 -q redis-server /etc/redis/redis.conf &
Redis is safely restricted to 127.0.0.1, Tailscale is free to bind to the 6379 port on the mesh interface. Tailscale receives the encrypted WireGuard packets from other Akash deployments, decrypts them, and proxies them directly to Redis on localhost. Redis accepts the traffic because it appears to be entirely local.